Secure knowledge

Information security is critical to our businesses. The confidentiality of clients’ business and information remains one of our core standards, but somewhere along the way we have lost sight of what this means in practice. As legal businesses have grown and the amount of information being handled has exploded, there may be a danger that we assume we are acting in a secure and confidential way or that someone else is looking after this issue.
What is information security?
Information security is not just about IT security.
Information security is about ensuring the confidentiality, integrity and availability (think “CIA”) of information:
- Confidentiality: Protecting the confidentiality of information is perhaps the easiest to understand. Only those people who should know about something should have access to the information about it. As well as our professional obligations to maintain our clients’ confidentiality, there are regulatory obligations to consider – for example with the Market Abuse Directive and the data protection regime.
- Integrity: Information should be trustworthy. It should be protected from unauthorised changes to protect its value and evidential weight.
- Availability: To have value, information needs to be available when and where you need it. Imagine that you arrive at work tomorrow and find all your paper and electronic files are missing. We all need to know that the information we hold (our own and our clients’) is safe and recoverable.
It’s also worth touching on what we mean by “information”. While often the debate focuses on information/data in IT systems, in fact it’s much wider than that. “Information” here means anything and everything that can store or transfer information or data – from paper (how we store it, send it), to phone conversations, office security and our staff, who carry lots of information in their heads.
Why is information security important?
- Handling information is a core part of our business. As lawyers, nearly everything we do involves receiving, creating, amending, reviewing, sending, saving and filing information.
- It makes good business sense. Having good governance about how we handle information can help us manage other risks such as quality or client satisfaction, and even improve efficiency.
- It’s critical to our reputation. Any information security incident is likely to have a detrimental effect on our reputation, which is built on the trust that clients give to their lawyers to keep their information safe.
- Clients are demanding it. Tenders routinely require detailed information security responses.
- Regulators are issuing large fines for breaches. The FSA can issue unlimited fines and the Information Commissioner fines up to £500,000.
- Auditors are starting to check it. Financial audits now often include questions around information security controls.
- And finally… your competitors are doing it. From an informal survey of IT directors at UK law firms, 60% are considering or have already certified against the international standard on information security.
Some scary examples
Barely a week goes by without some news of an organisation being hacked, fined or losing confidential data.
In May 2011 Sony hit the news after a vast amount of customer data was compromised (100 million customers’ details), and in March 2011 the global IT security firm, RSA, was hacked and information that could be used to access corporate and government networks was stolen.
In November 2010, Hertfordshire County Council was fined £100,000 for breaching the Data Protection Act by sending faxes with sensitive information to the wrong recipients. And A4e (an organisation that provides legal advice) was fined £60,000 for losing an unencrypted laptop (stolen from an employee’s locked house) with the details of thousands of people on it.
Law firm ACS:Law made the news last September when its participation in a scheme to target suspected copyright infringers by sending demand letters was thrust into the spotlight. It became a target itself and hackers stole the details of 13,000 people to expose what ACS:Law was doing. Aside from negative press and a fine from the Information Commissioner, the court cases it started have been abandoned and ACS:Law has ceased trading.
In August 2010, Zurich Insurance was fined £2.27 million by the FSA for losing the personal details of 46,000 customers Zurich shared with a supplier. The supplier was not managing data properly and Zurich didn’t know that the information had been lost until a year later.
In April 2009, Britain’s most senior anti-terrorist policeman, Assistant Commissioner Bob Quick, resigned after top secret documents under his arm – with the papers facing out towards the waiting press – were photographed.There are dozens of other examples.
A 2010 PWC survey carried out for Infosecurity Europe found that 92% of large organisations reported security incidents in the previous year, and 46% had confidential data lost or leaked. See the survey results at: www.pwc.co.uk/eng/publications/isbs_survey_2010.html
What should we take from the examples and this survey? Simply that law firms are not immune from such incidents, and if you think you’ve not had any information security incidents, you are probably just not finding out about them!
Positive action
Effective management of information security risks starts at the top, with the culture of the organisation. Management buy-in is vital, backed up by allocating responsibility at a senior level for overseeing the implementation of information security measures.
While IT is a key element in any modern information security policy, it should not be seen as an IT team responsibility. Information security is an issue for the whole business and should be managed like all the other business and regulatory risks.
A general risk management practice is critical. This includes having an agreed way of managing and recording risks in your business, for example an up-to-date and considered risk register.
In information security there are some good standards you should consider. In particular, International Standard ISO27001 (www.bsigroup.com/en/Assessment-and-certification-services/management-systems/Standards-and-Schemes/ISO-IEC-27001/). This is the standard most commonly referenced by clients, and many firms say they will comply with it, even if not working towards certification.
There is also a specific set of standards around how you handle payment card information – if your firm takes payment by credit or debit card, you need to read up on the PCI DSS standard (www.pcisecuritystandards.org).
The next step is to implement some sensible controls. You will find that you probably already have lots of the controls you might need, including:
- Policies and procedures – including an information security policy, an acceptable use policy, starters and leavers processes, a process for logging security incidents etc.
- Technical controls – for your IT such as firewalls, anti-virus software and strong passwords.
- Physical controls - that protect your buildings, your files, your IT and any sensitive information you have.
- Training and awareness controls - to help highlight and remind people why this is important.
Once you have in place the controls you need, you must review them regularly to make sure they are effective. It’s a common mistake for people to think that having a control in place is enough by itself, but how do you know if a control is working or is effective? For example: a lock on a door is a physical control – but you don’t know whether the door is actually locked (or is propped open by a box of deeds) if you don’t check.
The key to good security is people, so raising awareness about the issues and changing behaviours is essential (if difficult, especially with the myriad of other risk and compliance issues vying for attention).
Information security is ultimately everyone’s responsibility, and we need to get this message across to build secure ways of working into everyone’s day job.
Practical steps to take now
Finally, here are some thoughts and ideas you can use right away, as well as thinking over the bigger picture.
- Make sure information security is on your risk agenda. Having all risk areas managed together can significantly help with the administrative burden, and having a single approach to risks makes a coherent approach easier.
- Acknowledge that information security is not just about IT. If you only focus on IT security you will miss the key issues around people, premises and paper.
- Review/audit your suppliers. Remind yourself about what information you exchange or share with suppliers. This includes cleaners, shredding contractors, outsourced functions.
- Start an awareness campaign now. It’s a long road!
- Get the basics right and keep it simple. Make sure your key policies are in place and that you know what your key risks are.
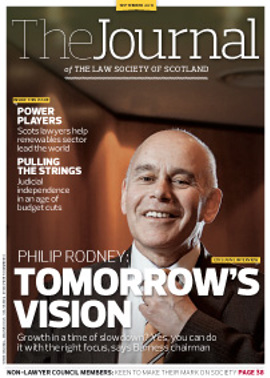
In this issue
- Maxwell Fyfe and the origins of the ECHR
- Introducing the European Law Institute
- Social media are here to stay
- Property points
- Paving the way for a new approach to elderly care
- Fair trial for the European Court of Human Rights
- Stalking: the hidden dangers, the silent crime
- Paul Wade: An appreciation
- Opinion
- Book reviews
- Reading for pleasure
- Council profile
- President's column
- Finger on the pulse
- Sharper focus
- The ties that bind
- Trawling for revenue
- The generation game
- Through the hoops
- Directors: to be, or not to be?
- Shoe stoppers
- Selection blues
- Conference calling
- ARTL: is there a fix?
- Building a better Buildmark
- Secure knowledge
- Key changes in compliance
- Guarantee Fund costs change
- Law reform update
- Strangers in the House
- Property points (1)
- Ask Ash
- Debt and asset recovery specialism goes live